Curmudgeonly Comments
I’ve been blogging for quite a long time, under several different names. This blog collects my computer-related posts.
Posts by Tag
Posts by Date
-
What Were You Thinking, Patreon?
So, a couple of days ago (September 8th, to be exact) Patreon laid off their entire five-person security team. WTF? The linked article goes on to say,
-
Update Zoom on Mac ASAP
According to this article posted yesterday on Ars Technica, there is a major security hole in Zoom for the Mac. Zoom issued a security bulletin on Saturday. The article suggests that you should download the update directly from Zoom or click on your menu bar options to “Check for updates” rather than waiting for the auto-update, although if you’ve already updated since Saturday you’re probably ok.
-
Trojan Source
This post in Krebs on Security describes an unusual and potentially very dangerous attack technique that can be used to sneak evil code past code reviews and into the supply chain. Briefly, it allows evildoers to write code that looks very different to a human and a compiler. It should probably come as no surprise that it involves Unicode, the same coding standard that lets you make blog posts that include inline emoji, or mix text in English and Arabic.
-
What happened to facebook yesterday?
If you're sensible enough not to use Facebook, WhatsApp, or Instagram, or to have set up "log in with Facebook" on any site you use regularly, you might not have noticed that they all disappeared from the internet for about six hours yesterday. Or if you noticed, you might not have cared. But you might have read some of the news about it, and wondered what the heck BGP and DNS are, and what they had to do with it all.
-
Public Service Announcement: Recent leaks and other news
1. The entirety of Twitch has reportedly been leaked: source code, user payouts, hashed passwords. Change your password RIGHT NOW.
-
Finding ELIZA
Note: Despite being posted on a Saturday and a title that includes the name of a a character from a well-known musical, this is not a Songs for Saturday post. It doesn’t have anything to do with fish, either.
-
RIP Fry's Electronics -- the end of an era
Today I was shocked to read that Fry's Electronics has gone out of business, as of midnight last night (February 24th). Their web page has the announcement:
-
Dependency Confusion
I've always been a little uncomfortable about build systems and languages that start the build by going out to a package repository and pulling down the most recent (minor or patch) version of every one of the package's dependencies. Followed by all of their dependencies. The best-known of these are probably Python's
pippackage manager, Javascript'snpm(node package manager), and Ruby'sgems. They're quite impressive to watch, as they fetch package after package from their repository and include it in the program or web page being built. What could possibly go wrong? -
Curmudgeon Thinks Out Loud
...about disk partitioning. Content warning: rather specialized geekness. If that's not something you're into, you might want to skip this.
-
The Curmudgeon Contemplates Keyboards
For the last week or two my external keyboard has been flaking out -- dropping keystrokes, and occasionally barfing out a string of repeats. The cats, of course, know nothing about this. Or will admit to nothing, in any case. So yesterday, after determining that a blast of canned difluoroethane wasn't going to fix it, I finally started to think seriously about replacing it.
-
Troubleshooting Sable's SSD
Early last Sunday afternoon I noticed that the battery-charge indicator had vanished from (main laptop)Sable's Gnome panel. (That's sort of like the row of icons and such you see along the bottom of the screen on a Mac, except that I've configured it to go vertically down the left-hand edge, where it doesn't reduce the hight of my browser window too much.)
-
PSA: Patch your Windows DNS server
If you happen to be running a Windows DNS server, I hope you have automatic updates enabled. Today's security update fixes CVE-2020-1350, also known as SigRed: A 17-year-old 'wormable' vulnerability for hijacking Microsoft Windows Server. I think that title kind of says it all, doesn't it? For the record, it's a heap-based buffer overflow that can be triggered by a malicious DNS query, and it's described as "wormable", with a CVSS base score of 10.0. Wormable means that it can propagate itself and spread exponentially to other vulnerable servers.
-
Ripple20
This one is pretty wild. Ripple20 is a set of 19 zero-day vulnerabilities in
a widely used low-level TCP/IP software library developed by Treck, Inc.
It gets its name because its position in the supply chain allowed the library with its vulnerabilities to ripple outward through hundreds of software and hardware vendors, and from there into hundreds of millions (maybe more) of devices. Printers, UPSs, infusion pumps, industrial control devices, ... any kind of thing in the Internet of Things that has a network connection. -
Why, and How to, Secure your S3 Storage
If you've ever looked into cloud storage (like for backups -- you do make backups, right?) you will recognize Amazon's Simple Storage Service, otherwise known as S3. It was the first of the Amazon Web Services to be released, in 2006. It's cheap ($0.023 per GB per month for up to 50TB, after which you get a bit of a discount), extremely reliable, and secure.
-
Patch your Windows 10 boxes.
If your Windows 10 boxes -- all of them, both desktops and servers, didn't apply the update that came out Tuesday, go do that now. You can chase the references below while the update is downloading.
-
Update Firefox NOW
Unlike my post Wednesday, this is one you should do Right Now(TM) if you have Firefox installed and aren't getting automatic updates. And even if you're getting updates automatically, you should check your version if you haven't updated since Wednesday. This vulnerability is being actively exploited in the wild.
-
SHA-1 is a SHA-mbles
I haven't put on my curmudgeon's hat in way too long. This isn't going to be a very long post, and if you don't know what a hash function is and what it's used for, all you need to do is make sure you're keeping up with security upgrades. Modern web browsers are already safe, and have been for the last three years or so; if you're still using a browser older than that, you should upgrade it. Some other programs in common use are not safe yet, so watch for security upgrades in the coming months.
-
Sable and the turtles: laptop configuration made easy
I recently bought a new-to-me Thinkpad X230, and in keeping with my ongoing theme of naming thinkpads after their color, I called it Sable, which in addition to being the heraldic name for the colour black is also a small dark-brown animal in the mustelid (weasel) family.
-
Laptop Lust
Wherein the curmudgeon cogitates out loud, and solicits suggestions.
-
Holding git repos for ransom - WTF?
Okay, this one's a bit weird. Apparently A hacker is wiping Git repositories and asking for a ransom (of 0.1 Bitcoin). Apparently it was done by scanning the entire web for
/.git/configfiles and mining those for credentials (including access tokens and URLs of the formhttp://user.password@victim.com. The hacker "replaced" the contents of the repository with a ransom demand. -
Armagadd-on 2.0
If you were using Firefox any time after midnight UTC on Star Wars Day (May the 4th), you probably noticed that all your add-ons were disabled, with the unhelpful message: "... could not be verified for use in Firefox and has been disabled". If you're reading this before 9am or so Pacific time on the 4th they may still be.
-
Git for Poets (and other writers): part 1
In my previous curmudgeon post, Writing Without Distractions, I gave version control only a brief mention, and promised a follow-up post. That would be this one. This post is intended for people who are not in the software industry, including not only poets but other writers, students, people who program as a hobby, and programmers who have been in suspended animation for the last decade or three and are just now waking up.
-
Writing Without Distractions
A few years ago I read an article about how to set up a Mac for distraction-free writing. I can't seem to find it anymore (okay, some rather large value of "a few"), but "there's an app for that" now. Many writers on my reading list are talking about distraction-free writing tools like iA Writer (seems to be the one people are most impressed by at the moment) and FocusWriter (free and cross-platform). There's even an Emacs mode.
-
Git: The other blockchain
Part 1: Blockchain
Blockchain is the technology behind Bitcoin and other cybercurrencies. That's about all anyone outside the software industry knows about it; that and the fact that lots of people are claiming that it's going to transform everything. (The financial industry, the Web, manufacturing supply chains, identity, the music industry, ... the list goes on.) If you happen to be in the software industry and have a moderately good idea of what blockchain is, how it works, and what it can and can't do, you may want to skip to Part 2.
-
This Week in Social Media
Interesting couple of articles on Ars Technica:
-
Yet Another Data Breach
It's getting so that data breaches aren't news anymore unless they're huge. The Gizmodo article calls it The Mother of All Breaches, exposing 773 million email addresses and 21 million passwords. There's a more complete post by Troy Hunt: The 773 Million Record "Collection #1" Data Breach. Hunt is the person behind the Have I Been Pwned website. That should be your next stop -- it lets you check to see which of your email addresses, usernames, and passwords have appeared in any data breach.
-
Privacy Tips
Some day I ought to put together a comprehensive list of privacy-related links. This is not that list; it's just a few of the links that came my way recently, in no particular order.
-
PSA: WA Emergency Numbers
From king5.com :
-
PSA: Centurylink outage
Last night around 11pm I was awakened by an alert on my phone telling me that 911 service was down, and giving me an alternat number to call. By morning, it was clear that it wasn't a local problem. A quick search showed that the problem was caused by CenturyLink, which tweeted, blaming it on a
a network element that was impacting customer services
and saying that they estimated it would be fixed in about four hours. -
Multitasking
Most humans multitask rather badly -- studies have shown that when one tries to do two tasks at the same time, both tasks suffer. That's why many states outlaw using a cell phone while driving. Some people are much better than others at switching between tasks, especially similar tasks, and so give the appearance of multitasking. There is still a cost to switching context, though. The effect is much less if one of the tasks requires very little attention, knitting during a conversation, or sipping coffee while programming. (Although I have noticed that if I get deeply involved in a programming project my coffee tends to get cold.) It may surprise you to learn that computers have the same problem.
-
Learn Enough to be Dangerous
Recently I started reading this Ruby on Rails Tutorial by Michael Hartl. It’s pretty good; very hands-on, and doesn’t assume that you know Ruby (that’s a programming language; Rails is a web development framework). It does assume that you know enough about software development and web technology to be dangerous. And if you’re not dangerous yet,…
It points you at a web site where you can learn enough to be dangerous. Starting from knowing nothing at all.
-
Here There be Posts
I have spent the last couple of days backfilling the blog with a selection of relevant posts from my Dreamwidth/Livejournal archive. By the time I was done this afternoon, I had a script that does most of the work of importing, and 20-odd new posts. (Well, old posts. New here.) A little manual editing is still required to correct the occasional tag that’s unique to the original blogging engine. They cover much of my recent writing on security, software, and the web.
-
The Apache .htaccess vulnerability
There’s an article about a security problem getting a bit of attention lately, Apache Access Vulnerability Could Affect Thousands of Applications. Sounds really scary. Here’s a better article about it, Zero-day in popular jQuery plugin actively exploited for at least three years. Looking at those titles you might think that the problem is either with a jQuery plugin, or Apache’s
.htaccessfiles. It’s neither. The real situation is more complicated. You might think that if you’re not using this plugin on your website, you’d be safe. You’d be wrong. You might think that patching the plugin, or the Apache web server, would solve the problem. You’d be wrong about that, too. The real problem is still there, waiting to bite you in the tail. If you don’t have a website, or don’t allow file uploads, you can stop reading now unless you’re curious. If you do, stick around (or jump to the last section if all you want is the fix). -
Further Adventures in Hyperspace
You may remember from my previous post about Hyperviewer that I’d been plagued by a mysterious bug. The second time the program tried to make a simplex (the N-dimensional version of a triangle (N=2) or tetrahedron (N=3), a whole batch of “ghost edges” appeared and the program (quite understandably) blew up. I didn’t realize it until somewhat later, but there were ghost vertices as well, and that was somewhat more fundamental. Basically,
nVertices, the field that holds the number of vertices in the polytope, was wildly wrong. -
Adventures in hyperspace (and JavaScript)
This post is about Hyperviewer, an update of a very old demo program of mine from 1988 that displays wireframe objects rotating in hyperspace. (Actually, anywhere between four and six dimensions.) Since this is 2018, I naturally decided to write it in JavaScript, using Inferno and SVG, and put it on the web. It was a learning experience, in more ways than one.
-
Transplanting Subtrees With git
If you have a lot of projects in separate
gitrepositories, you're eventually going to want to do some refactoring and put some a subtree or two into their own repository so that you can reuse them. (If everything is under the same repository, you probably moved your tree from Subversion or CVS, and you'll want to split it up. These techniques work for that, too.) -
PSA: Data breach at Newegg
TL;DR: if you bought anything from Newegg between August 14th and September 18th, call your bank and get a new credit card. You can find more details in these articles: NewEgg cracked in breach, hosted card-stealing code within its own checkout | Ars Technica // Hackers stole customer credit cards in Newegg data breach | TechCrunch // Magecart Strikes Again: Newegg in the Crosshairs | Volexity // Another Victim of the Magecart Assault Emerges: Newegg
-
Why Singly-Linked Lists Win*
Singly-linked lists, like the ones found in Lisp, have a lot of advantages. But first, let’s back up a little and start with doubly-linked lists, of the sort that one finds in Java and most other object-oriented languages.
-
Progress is being made
The site is almost presentable at this point; I have started to bring over some blog entries/articles that were originally published elsewhere. Most of these were originally published in my personal blog, so they should be considered cross-posts. Articles that form a series can be grouped using tags.
-
Next steps
It’s time to figure out what to do next, in particular about ssavitzky.github.io (ss.g.io for short) and computer-curmudgeon.com (c-c.com). Right now they are simply mirroring one another; it’s time to differentiate them, so that Curmudgeon is about my (incipient) consulting business, and the GitHub site is about software development. Some provision also has to be made for my “resume” site, Stephen.Savitzky.net (S.S.net – the capital letters distinguish it from my “personal” site, steve.savitzky.net). This post is me thinking out loud about what to do about that.
-
PSA: Security
Actually two PSAs.
-
Jekyll without GitHub
Jekyll works just fine on my laptop. If I continue hosting this site on my own web host, I don’t have to restrict my Jekyll configuration to what GitHub gives me – that opens up the full range of available plugins. It also means that I can drag over some content from other places on the server, if I want to. Like my resume? Yeah, that.
-
Uploading and showing an image on DW
This started out in a comment, but I think enough people may be struggling with DW's relatively new image upload feature that it's worth making it into a post. And it's a good excuse for posting.
-
Setting up gojekyll
My shared hosting service doesn’t like users to install their own copy of Ruby unless they have their own virtual host – Ruby tends to be a memory hog, especially when it’s running something like Jekyll. Fortunately, there’s an alternative:
gojekyll, a Jekyll clone written ingo. (That’s a programming language – it’s often called “golang” to distinguish it from the Japanese board game.) It’s extremely fast and lightweight. My shared hosting service doesn’t have go installed, but getting it up and running is easy. -
Under Construction
Please excuse our dust; we’ll get the construction debris out of the way soon.
-
Building a GitHub Pages website, part 7
Wherein we speak of tags, categories, and content. We also touch briefly on the general inadequacy of GitHub’s implementation of Jekyll, and at greater length on the need for a build system.
-
Building a GitHub Pages website, part 6
Wherein our intrepid blogger reflects on the current state of the site. At this point, things are pretty much the way he wants them.
-
Building a GitHub Pages website, part 5
Wherein our intrepid programmer gets a nice feeling of accomplishment. There is a sidebar, and he explains how to make one of your own. Sort of.
-
Building a GitHub Pages website, part 4
Overriding a theme Wherein our intrepid programmer decides to develop his new Jekyll theme by taking an axe to the best example he could find, which happens to be the default.
-
Building a GitHub Pages website, part 3
Read-Mostly Wherein our intrepid programmer begins to get a bad feeling about this.
-
Building a GitHub Pages website, part 1
Step by step. Wherein our intrepid programmer embarks on the seemingly simple journey from a straightforward but boring and hard-to-maintain website written in raw HTML, to a shiny new website based on Jekyll and hosted on GitHub Pages. We’ll see how simple it really is in the next installment or two.
-
Building a GitHub Pages website, part 2
… and one step back Wherein our intrepid programmer begins to run into difficulties. This will be an ongoing, um… theme in most of the rest of the series.
-
Scripting Languages
Today in my continuing series on programming languages I'm going to talk about "scripting languages". "Scripting" is a rather fuzzy category, because unlike the kinds of languages we've discussed before, scripting languages are really distinguished by how they are used, and they're used in two very different ways. It's also confusing because most scripting languages are interpreted, and people tend to use "scripting" when they should be using "interpreted". In my opinion it's more correct to say that a language is being used as a scripting language, rather than to say that it is a scripting language. As we'll see, this is particularly true when the language is being used to customize some application.
-
Blog posting software planning
In comments on "Done Since 2018-07-15" we started having a discussion of mirroring and cross-posting DW blog entries, and in particular what my plans are for implementing personal blog sites that mirror all or some of a -- this -- Dreamwidth journal.
-
PSA: Venmo users check your privacy settings!
If you're using the popular social/money-transfer phone app Venmo check your privacy settings!! It seems that the default is that every transaction you make is public! It is difficult for me to express just how broken this is. In case you're having trouble grasping the implications, just go to PUBLIC BY DEFAULT - Venmo Stories of 2017. There you will find profiles of five unsuspecting Venmo users -- one of them is a cannabis retailer -- whose transactions were among the over two hundred thousand exposed to public view during 2017.
-
Languages: Imperative, Object-Oriented, and Functional
Even if you're not a programmer (and most of the people I expect to be reading this aren't) you've probably heard one of your geek friends mentioning "object-oriented" programming. You might even have heard them mention "functional" programming, and wondered how it differs from non-functional programming. The computer curmudgeon can help you.
If you are a programmer, you probably know a lot of this. You may find a few items of historical interest, and it might be useful explaining things to the non-programmers in your life.
-
HTML for Poets: Some simple magic
Here are a couple of little tricks that may keep you from tearing your hair out in frustration, and in any case will make your posts look better.
-
Git and GitHub, with a side of Microsoft
If you develop software and haven't just returned from the moon, you've undoubtedly heard that GitHub is being acquired by Microsoft. Depending on your affiliations you might be spelling "being acquired by" as "selling out to". The rest of you are probably wondering what on Earth a GitHub is, and why Microsoft would want one. Let me explain.
-
Computer Languages: compiled, interpreted, and assembled.
A few months ago while waiting for a ferry with my sister I mentioned a programming language called Elm, which I've been particularly interested in because it's a functional language that compiles into Javascript. Her response, predictably, was something like "I have no idea what you just said. What does 'compiles' mean?" So I explained the difference between compilers and interpreters, and a few other things about programming languages, and she said that it was the first time anyone had explained how programming languages work in a way that made sense to her. In the back of my mind, I thought it might someday make an interesting blog post. So here it is.
-
efail
If your mail client automatically decrypts mail, read this!
-
HTML for Poets: The Joy of Static Sites
Recently I read a couple of blog posts that set me thinking in some interesting directions. Like most of the things I find on LinkedIn, they were mostly a little annoying, with a few good points. For example, Why You Should Decisively Reject Using Wix gives a lot of good reasons not to use Wix, which is a free website builder and host that lets you throw together a website in half an hour by simply picking a template and dragging and dropping things into it. What's not to like, right? Well,...
-
Meltdown and the Spectre of Speculation
TL;DR: Patch your computer NOW! (Or as soon as you can, if you're running Windows or Ubuntu and reading this on Monday -- the official release date for this information was supposed to have been Tuesday January 9th.)
-
Meta: How to.do it
A few days ago I got a comment on my weekly post that went Oohh, you're doing what looks to me like a bullet journal? Only online. So I wrote a quick explanation. And then I realized that I might be doing something unusual, that I ought to write up in more detail. So here you are:
-
[I wrote a thing] Xmonad (part 2 of several)
(You may want to start with Part 1)
Xmonad is a tiling window manager. That means that, with very few exceptions, it lays out all of the windows in your workspace so that they completely fill the screen. You can have multiple layouts, and flip between them with a single keystroke. You can bring a workspace (there are 9 by default, but you can add more) to your screen with a single keystroke, or send a window to a workspace.
And the whole thing is configured using a text file that is actually a program, written in the functional language Haskell. I'll get to that later.
-
[I wrote a thing] xmonad (part 1 of several, incomplete)
As I mentioned about a week ago, I've been trying to write more. And since my current obsession is a program called xmonad, well, ...
This is incomplete: it's about the first day's worth (I've been trying to write about 500 words per day). Comments and suggestions are, of course, welcome.
-
PSA: PHP Must Die
Advisory 01/2014: Drupal - pre Auth SQL Injection Vulnerability
A "highly critical public service announcement" from Drupal [LWN.net] "Automated attacks began compromising Drupal 7 websites that were not patched or updated to Drupal 7.32 within hours of the announcement of SA-CORE-2014-005 - Drupal core - SQL injection. You should proceed under the assumption that every Drupal 7 website was compromised unless updated or patched before Oct 15th, 11pm UTC, that is 7 hours after the announcement."
Impressive. I think this is an appropriate place to quote one of my father's aphorisms: "A locked car with an open window is NOT a locked car."
If PHP is your open window, you may as well leave the keys on the dashboard where they're easy to see.
-
Clearing my tabs: Don Marti on Google Chrome
Don Marti www/google-chrome.htmlThe idea of tabs being first class citizens makes a lot of sense, but why have a sub-window-manager that just manages browser windows in tabs, when you could have a tabbed window manager that can manage everything? I might want a browser and a spreadsheet to share a tab.
-
So much for that idea
From this post by
, a cautionary tale of the of relying on third-parties to store your important files and email: When Google Owns You. One of my coworkers had an equally bad experience with Netscape Calendar: one day it was just gone. Not only had they cancelled the service, but they'd deleted all the user data. They had been careful not to tell their customers of this plan, because they "didn't want anyone to complain."
I'd been contemplating switching some of my domains over to Google for email -- Dreamhost makes it easy to set that up. Maybe not.
Yeah, almost all of my websites are third-party-hosted now. But the hosts are nothing but a mirror for the various internal working directories. And they're going to stay that way. If I can figure out how to do that with some Google's services, I may consider using a few of them.
-
2,000 Wikipedias per year
The title comes from "Gin, Television, and Social Surplus" by Clay Shirky. Somebody asked him "where do people find the time?" to create something like Wikipedia. Wikipedia -- the whole thing, articles and edits and talk pages and translations -- represents some 100 million hours of human thought. TV watching, in the US alone, amounts to some 200 billion hours every year. That's 2,000 Wikipedia projects every year.
Shirky points out that, in the years spanned by the Industrial Revolution, "The transformation from rural to urban life was so sudden, and so wrenching, that the only thing society could do to manage was to drink itself into a stupor for a generation." Gin, and more gin. "And it wasn't until society woke up from that collective bender that we actually started to get the institutional structures that we associate with the industrial revolution today."
The equivalent, in the latter half of the 20th Century, was television. Society is only now waking up from that collective bender. What are you doing with your free time?
I'm not watching TV much these days. Nor movies. Nor listening to radio, even during my commute. Nor even reading books and magazines. I am still drugging myself -- I'm a product of my generation, not yet completely adapted to life in the 21st Century -- but my drug of choice these days is mostly LJ. A decade ago it was Usenet. At least my current drugs are interactive.
Sometimes, my current drugs create things that last. Some of my LJ content finds its way onto my website; my songs and essays are already there. I'm working on it. I came out with a CD over the course of two or three years in, basically, the time I saved by not watching TV. I ought to try not reading LJ so much.
(First brought to my attention in this post by
; recently seen on techdirt as well.) -
Privacy and security
Good post on privacy vs. security, with reference links, posted by
. Via . In a Jan. 21 "New Yorker" article, Director of National Intelligence Michael McConnell discusses a proposed plan to monitor all -- that's right, *all* -- Internet communications for security purposes, an idea so extreme that the word "Orwellian" feels too mild.
This is really just a matter of formalizing what's been widely suspected for years: that the NSA has been monitoring all the phone and Internet communications it can get to.
"The land of the free and the home of the brave..."
Yeah, right. Try this version.
-
Going offline
Excellent post by Don Marti on becoming more productive by going offline. Git (distributed version control, basically syncing on steroids), ikiwiki (offline-rendered wiki), blosxom (offline-rendered blog), and more. It's related to a lot of what I've been saying about keeping control of your own data. In essence, what you want to do is to separate writing from publishing.
-
Security?
Techdirt: TSA Staffer Hires Buddies To Build Insecure Website For Folks Falsely On Watch ListWe've had so many stories of government computer systems or websites that have terrible security or are just useless (but expensive!) that it shouldn't surprise us to hear of another one. Yet, there's always someone who can go a step further. Witness the news that the TSA's website for individuals who find themselves incorrectly on the security watchlist has been found to be insecure, with hundreds of falsely accused travelers exposing personal details by using the site. Even better, it turns out that the company that was hired to build the site got the job in a no-bid contract (meaning there wasn't any competition -- it was just chosen) and the guy responsible for figuring out who to hire just so happened to have been a former employee at that company. So, basically, what happened was that a guy who had taken a job at the TSA hired his former coworkers, with no competition for the job and apparently little oversight, to just build a website that turned out to be insecure. And, of course, without any oversight, it took months before anyone even noticed the site was insecure. And, remember, that this is the TSA we're talking about here -- an organization who's main concern is supposed to be security. I feel safer already.
Why am I not surprised by this? The original article is on InformationWeek. -
Making it
"If you want something to get done, ask a busy person to do it." I haven't been accomplishing much lately, so obviously I'm not busy enough.
There are several seemingly-unrelated projects going on in the household at the moment: I'm starting my next album, the
is starting an HTML class, the servers are getting re-organized, and people have been after the to write a cookbook. Meanwhile I've been thinking about writing my blog locally and mirroring it up to LJ. They're all more closely related than one might think.
-
More analysis of Facebook's privacy fiasco
Freedom to Tinker » Blog Archive » Lessons from Facebook’s Beacon MisstepFacebook recently beat a humiliating retreat from Beacon, its new system for peer-based advertising, in the face of users’ outrage about the system’s privacy implications. (When you bought or browsed products on certain third-party sites, Beacon would show your Facebook friends what you had done.)
-
The Eternal Flame
xkcd: With Apologies to Robert Frost
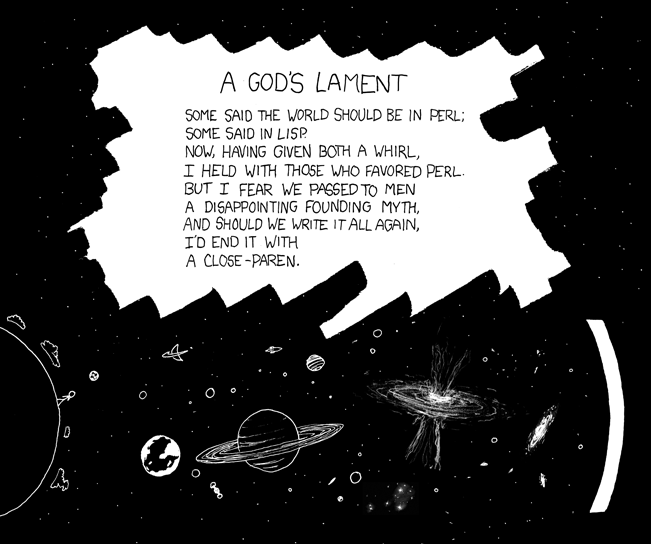
Somebody ping Kanefsky
-
Web service disaster planning
This blog post was written after an inquiry about Amazon's EC2 and S3 services, but it applies much more generally to anyone trying to run a business and depending on an outside service provider. LJ comes to mind, for example. Amazon's terms and conditions include the following disturbing paragraph, which I suspect is not at all unusual in such places:
We further reserve the right to discontinue Amazon Web Services, any Services, or any portion or feature thereof for any reason and at any time in our sole discretion. Upon any termination or notice of any discontinuance, you must immediately stop your use of the applicable Service(s), and delete all Amazon Properties in your possession or control (including from your Application and your servers). Sections 3, 5, 8 - 12, any definitions that are necessary to give effect to the foregoing provisions, and any payment obligations will survive any termination of this Agreement and will continue to bind you and us in accordance with their terms.
In other words, we can pull the plug on you at any time, on no notice at all, but you still have to pay us if you owe us any money.
Think about your web hosting service, your ISP, your online banking, web email provider, your web storefront provider, your blogging service (gestures toward SixApart),... Which of them have real SLA's (that's Service Level Agreements for us Luddites) and which have terms like Amazon's?
Now: which of them is your business depending on, and what are your disaster plans if they suddenly go belly-up, get taken out by the local flavor of natural disaster, or simply get distracted by the next shiny bubble-of-the-year and decide they don't want to play anymore?
Now, if you'll excuse me, I have to do some serious planning.
-
If you think that current web servers are bloated...
KLone - Embedded Web Server and SDKKLone is a fully-featured, multiplatform, web application development framework, targeted especially for embedded systems and appliances.
-
File formats for information exchange
This blog post by Eugene Spafford points out that
Microsoft Word:
- Is not a document interchange format -- it is not designed for document transport
- Is not installed on everyone's machine, nor available for everyone's machine
- Not all versions of Word are compatible with each other
- Results in huge, bloated, files for tiny content (such as memos)
- And of course, Word is commonly a vector of viruses and maicious hacks.
He includes a link to the (plaintext) "bounce message" that he uses to educate people who send him Word documents. Well worth a look.
Similar considerations apply to files produced by PowerPoint, Finale, Photoshop, and other programs. Open-source, cross-platform programs like Audacity and the Gimp aren't immune either: even when they're available cross-platform, you shouldn't use them for email.
If you're actively collaborating with somebody who you know is using the same program and version (I'm upgrading to Audacity 1.3; this isn't just a Microsoft problem by any means), by all means use that program's file format, but put it on a website and email the URL rather than trying to ship the whole darned thing in email. Many email systems will bounce big files anyway.
If you're sending a finished product, use plain text, HTML, or XML if at all possible. Other text-based standards include LaTeX for typeset documents and ABC for music. Images can be sent as PDF or JPEG, formatted documents as PDF, music notation as a zipped MIDI file, and sound files as FLAC or Ogg. But even here they're big enough that you'll want to put them on the web and email a link.
(via
.) ETA Oh, and if you're thinking this was inspired by a particular piece of email, or a particular blog post, it wasn't. Just seemed like a good reminder, especially now that I'm trying to put together a CDROM. -
The Mandelbear's Rough Guide to HTML
Since I've noticed that a couple of new folks have either joined LJ, or posted after a long absence, and since I just spouted off a comment describing the basic HTML tags, here's another take on it, with the rough edges smoothed off.
Here are the essential tags for LJ. You can get away with nothing but these, and let LJ's automatic formatting take care of everything else.
-
Protecting your privacy on line
AOL publishes database of users' intentions | The Register -
Crash-only software
Crash-Only Software:
Abstract:
Crash-only programs crash safely and recover quickly. There is only one way to stop such software -- by crashing it -- and only one way to bring it up -- by initiating recovery. Crash-only systems are built from crash-only components, and the use of transparent component-level retries hides intra-system component crashes from end users. In this paper we advocate a crash-only design for Internet systems, showing that it can lead to more reliable, predictable code and faster, more effective recovery. We present ideas on how to build such crash-only Internet services, taking successful techniques to their logical extreme.
Sent to me by Aahz, who found the link on a Python mailing list. Intriguing, but really only applies at the lower end of the high-reliability spectrum. For software to get to the point where I'd trust it with my life passing a truck on a two-lane road with oncoming traffic, I'd expect proof-of-correctness on some little single-tasking microcontroller, with all of its state in either registers or ROM.
-
Bad web design, 2005
Jakob Nielsen has published his list of the Top Ten Web Design Mistakes of 2005.
On the whole I agree with him, especially on the subject of fixed font sizes and frozen layouts. Not that it's going to do any good, of course.
subscribe via RSS